Eco: Polygraphies
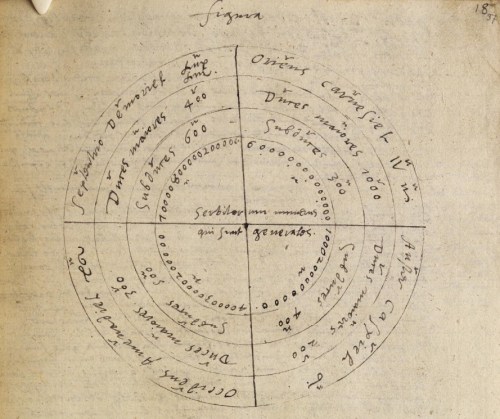
John Dee (1527-1609), an excerpt from Steganographiae, aka Peniarth MS 423D, astrological texts in Latin, 1591. Steganographiae was originally composed by Johannes Trithemius in the 1490’s. Infamous as a work of cryptography, this excerpt was copied by hand by Dr. Dee. Peniarth MS 423D is held by the National Library of Wales. This file is made available under the Creative Commons CC0 1.0 Universal Public Domain Dedication. All rights are waived worldwide under copyright laws. This file can be copied, modified, and distributed with no permissions required.
“Steganographies were used to cipher messages in order to guarantee secrecy and security. However, even though disregarding many terminological details (or differences) used today by the cryptographers, one must distinguish between the activity of coding and decoding messages when one knows the key, or code, and cryptoanalysis (sic); that is, the art of discovering an unknown key in order to decipher an otherwise incomprehensible message.
Both activities were strictly linked from the very beginning of cryptography: if a good steganography could decode a ciphered message, it ought to allow its user to understand an unknown language as well.
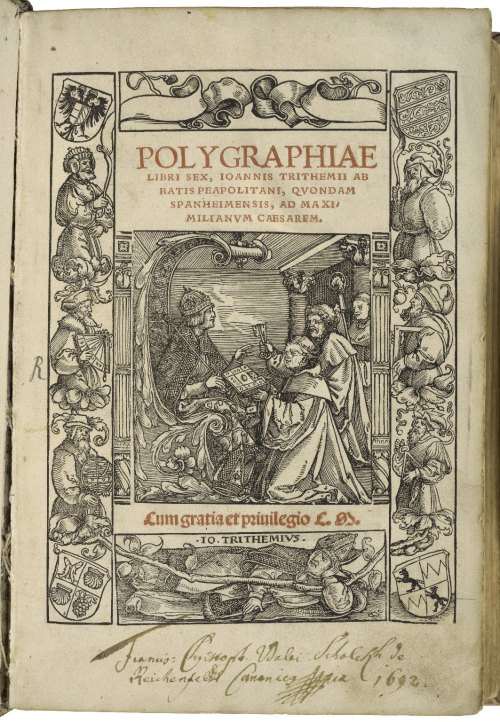
When Trithemius wrote his Polygraphiae, which was published in 1518, before his Steganographia, and did not earn the sinister fame of the latter work, he was well aware that, by his system, a person ignorant of Latin might, in a short time, learn to write in that “secret” language (1518: biiii) (sic).
Speaking of Trithemius‘ Polygraphia, Mersenne said (Quaestiones celeberrimae in Genesim, 1623: 471) that its “third book contains an art by which even an uneducated man who knows nothing more than his mother tongue can learn to read and write Latin in two hours.”
Steganography thus appeared both as an instrument to encipher messages conceived in a known language and as the key to deciphering unknown languages.
In order to cipher a message one must substitute the letters of a plain message (written in a language known by both the sender and the addressee) with other letters prescribed by a key or code (equally known by sender and addressee).
To decipher a message encoded according to an unknown key, it is frequently sufficient to detect which letter of the encoded message recurs most frequently, and it is easy to infer that this represents the letter occurs most frequently in a given known language.
Usually the decoder tries various hypotheses, checking upon different languages, and at a certain point finds the right solution.
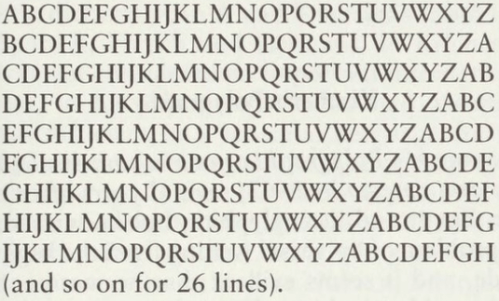
The decipherment is made, however, more difficult if the encoder uses a new key for every new word of the message. A typical procedure of this kind was the following. Both the encoder and the decoder refer to a table like this:
Umberto Eco, The Search for the Perfect Language, p. 195.
Now, let us suppose that the key is the Latin word CEDO. The first word of the message is encoded according to the third line of the table (beginning with C), so that A becomes C, B becomes D and so on.
The second words is encoded according to the fifth line (beginning with E), so that A becomes E and so on. The third word is encoded according to the fourth line, the fourth according to the fifteenth one . . . At the fifth word one starts the process all over again.
Naturally the decoder (who knows the key) proceeds in the opposite way.
In order to decipher without knowing the key, if the table is that simple and obvious, there is no problem. But even in cases of more complicated tables the decipherer can try with all possible tables (for instance, with alphabets in reverse order, with alternate letters, such as ACEG), and it is usually only a matter of time before even the most complex of codes are broken.
Observing this, Heinrich Hiller, in his Mysterium artiis steganographicae novissimum (1682), proposed to teach a method of learning to decipher messages not only in code, but also in Latin, German, Italian and French, simply by observing the incidence of each letter and diphthong in each language.
In 1685, John Falconer wrote a Cryptomenysis patefacta: or the Art of Secret Information Disclosed Without a Key, where he noted that, once someone has understood the rules of decipherment in a given language, it is possible to do the same with all the others (A7v).”
Umberto Eco, The Search for the Perfect Language, translated by James Fentress, Blackwell. Oxford, 1995, pp. 194-6.